In the last few months, as people have spent much more time at home due to COVID-19, doors have closed and laptops have opened.
The numbers reflect the fact that this international change in lifestyle has resulted in a rise in porn consumption, and along with it, something else: online scams.
Using tactics that are almost exactly like those of a Black Mirror episode, more people are receiving and falling for the latest twist of an old-time scammer tactic, sextortion.
What is sextortion?
Sextortion. As the name hints at, it’s a combination of “sex” and “extortion,” a term coined when these types of hoaxes first starting appearing around 2018. It’s a type of blackmail, and plays out something like this:
Someone checks their email and stumbles across a message from an unknown sender, or even what looks like an email sent from their own account. The sender claims to have hacked their computer. It’s written in poor English, but they post an old email password and the recipient’s phone number, just so the recipient knows they’re serious. They assert they have installed malware in the person’s device and have access to certain sensitive files or have hacked into their camera and microphone and have been recording them in some intimate situations. What do they want? They demand the email recipient immediately delivers on sexual content or favors, cash or—as is the trend lately—payment in cryptocurrency. In exchange, they promise to disappear, or simply refrain from sharing to the email recipient’s friends, family, and coworkers the intimate content they supposedly have. The email recipient has 24 hours to comply.
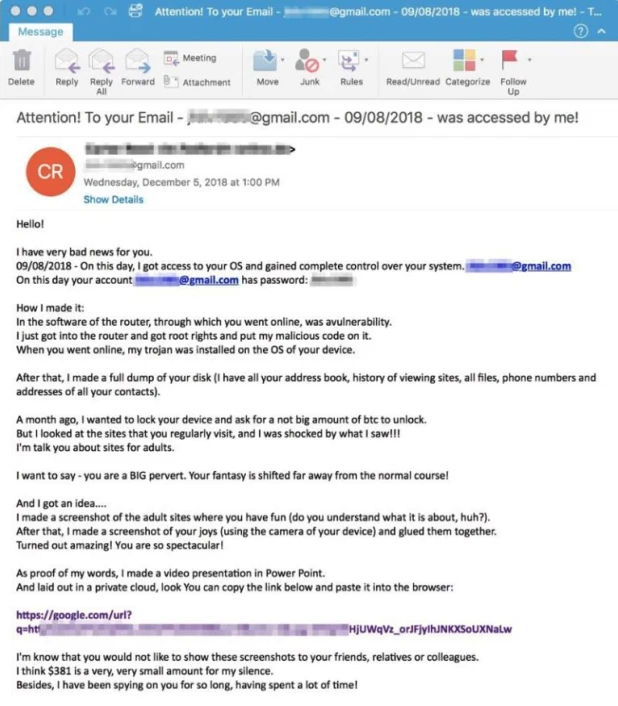
Here’s a real example of a sextortive email:
Scary, right?
According to many cybersecurity experts and government advisors, there’s generally no reason to be afraid this will happen to you. Because while the latest spike in this scam is from extorters claiming they have incriminating footage of consumers while visiting porn sites, in the majority of cases, it’s a bluff. They are playing to victims’ fear to the point where even those who don’t consume pornography can be shaken by the threats.
The personal data used to make their threats more credible like passwords or phone numbers are often bought from the dark web, where they have been sold after an old attack or data breach. Security experts recommend sites like “Have I Been Pwned” or Google’s Password Checkup Extension to detect if you’ve experienced a data breach.
In short: the sextortion emails are bogus, and if victims can take a step back from the fear, they might see it’s a very convincing scheme.
Does anyone buy it?
While extorters are keen to leverage the opportunity of scaring people who are spending more time at home and possibly consuming more porn, it seems that the results haven’t been as effective everywhere.
In Oregon, for example, the state Attorney General has stated that there are few people actually handing over money, in part because they don’t understand bitcoin or other cryptocurrencies the extorter may demand payment in.
All the same, the number of sextortion cases are on the rise, and have increased during the pandemic in states like New Hampshire and Oregon, but extended into Canada as well. This is also underpinned by the fact that, though few victims may pay up, it is still a lucrative business since the scam requires little technical effort and can easily reach many potential victims.
From a single campaign over the course of five months, close to $500,000 was made by criminals.
In fact, April 2020 saw a massive spike in bitcoin scams, which includes sextortion cases, according to a site dedicated to tracking and reporting bitcoin web addresses used by criminals. Compared to a relatively steady 3,000-4,000 reports recorded monthly since last, year, April saw the numbers jump thirteen times what they had been the month before, from 3,684 reports to almost 50,000.
But while the peak in these cases has shed light on this type of fraud, it certainly isn’t the first time sextortion scams have been found. They’ve been around for a few years, and are more common than many people think.
A new take on an old scam
Back in 2018, it was more common to see sextortion scams, but of a different type.
Led by overseas organized criminal gangs, scammers had two approaches: they would either connect with minors via social media platforms with a fake profile and convince them to send explicit images of themselves, then use those images against them through threats of even physical violence.
Or, the other method they would use is connecting with adults on what appeared to be normal webcamming sites. Women working for these groups would typically engage in video calls with their victim, and convince the person on the other side of the conversation—usually a guy—to record or send compromising videos or images, and then use them as blackmail. Yikes.
What to do if you’re (s)extorted
What can you do if you encounter one of these emails?
Experts and government agencies echo one another: don’t answer the email. The best idea is to delete the message, and contact your state consumer protection website if it exists, or the Federal Trade Commission or FBI, otherwise.
If you’ve sent money or personal information, or the email contains proof they have sensitive information, it’s definitely important to consider changing your password and submitting a report with the attorney general or local authorities.
Some legal services have recommended changing privacy settings on social media accounts to make friend lists private.
Your Support Matters Now More Than Ever
Most kids today are exposed to porn by the age of 12. By the time they’re teenagers, 75% of boys and 70% of girls have already viewed itRobb, M.B., & Mann, S. (2023). Teens and pornography. San Francisco, CA: Common Sense.Copy —often before they’ve had a single healthy conversation about it.
Even more concerning: over half of boys and nearly 40% of girls believe porn is a realistic depiction of sexMartellozzo, E., Monaghan, A., Adler, J. R., Davidson, J., Leyva, R., & Horvath, M. A. H. (2016). “I wasn’t sure it was normal to watch it”: A quantitative and qualitative examination of the impact of online pornography on the values, attitudes, beliefs and behaviours of children and young people. Middlesex University, NSPCC, & Office of the Children’s Commissioner.Copy . And among teens who have seen porn, more than 79% of teens use it to learn how to have sexRobb, M.B., & Mann, S. (2023). Teens and pornography. San Francisco, CA: Common Sense.Copy . That means millions of young people are getting sex ed from violent, degrading content, which becomes their baseline understanding of intimacy. Out of the most popular porn, 33%-88% of videos contain physical aggression and nonconsensual violence-related themesFritz, N., Malic, V., Paul, B., & Zhou, Y. (2020). A descriptive analysis of the types, targets, and relative frequency of aggression in mainstream pornography. Archives of Sexual Behavior, 49(8), 3041-3053. doi:10.1007/s10508-020-01773-0Copy Bridges et al., 2010, “Aggression and Sexual Behavior in Best-Selling Pornography Videos: A Content Analysis,” Violence Against Women.Copy .
From increasing rates of loneliness, depression, and self-doubt, to distorted views of sex, reduced relationship satisfaction, and riskier sexual behavior among teens, porn is impacting individuals, relationships, and society worldwideFight the New Drug. (2024, May). Get the Facts (Series of web articles). Fight the New Drug.Copy .
This is why Fight the New Drug exists—but we can’t do it without you.
Your donation directly fuels the creation of new educational resources, including our awareness-raising videos, podcasts, research-driven articles, engaging school presentations, and digital tools that reach youth where they are: online and in school. It equips individuals, parents, educators, and youth with trustworthy resources to start the conversation.
Will you join us? We’re grateful for whatever you can give—but a recurring donation makes the biggest difference. Every dollar directly supports our vital work, and every individual we reach decreases sexual exploitation. Let’s fight for real love: